Contents
What is MRT.exe?
To understand the term MRT.exe, let’s break it down step by step. MRT stands for Microsoft Windows Malicious Removal Tool. This tool is designed to detect and remove malicious software, such as viruses, malware, spyware, adware, and other harmful programs that can harm a computer system or compromise user data. It is a free program developed by Microsoft for the Windows OS.
Next, let’s discuss the .exe part. The .exe file extension indicates that the file is an executable file format. An executable file is capable of being executed or run by the operating system. In the case of MRT.exe, it is a program that, when opened, triggers the operating system to run the Microsoft Windows Malicious Removal Tool.
Functions of MRT.exe
As a post-infection removal tool, it is not designed to serve as a substitute for an anti-virus program. Microsoft also advises against using it as a replacement for proper anti-virus software. Here are some of its functions:
- The tool gets rid of only specific prevalent malware. This specific malicious software is a modest subset of all the malware that exists on the internet today.
- The tool eliminates malware from a computer that’s already infected. Antivirus software stops malware from running on a personal computer.
- The software concentrates on the detection and elimination of active malicious software. Active malware is malicious software that’s currently running on the PC.
When does MRT.exe become dangerous?
- MRT.exe could be malicious if you find it outside of your system32 folder (C:\Windows\System32 folder). You should delete it in this case according to Windows support.
- If it is located in a subfolder of the Windows folder for temporary files, the security rating is 86% dangerous.
- If it is located in a subfolder of the user’s profile folder, the security rating is 81% dangerous.
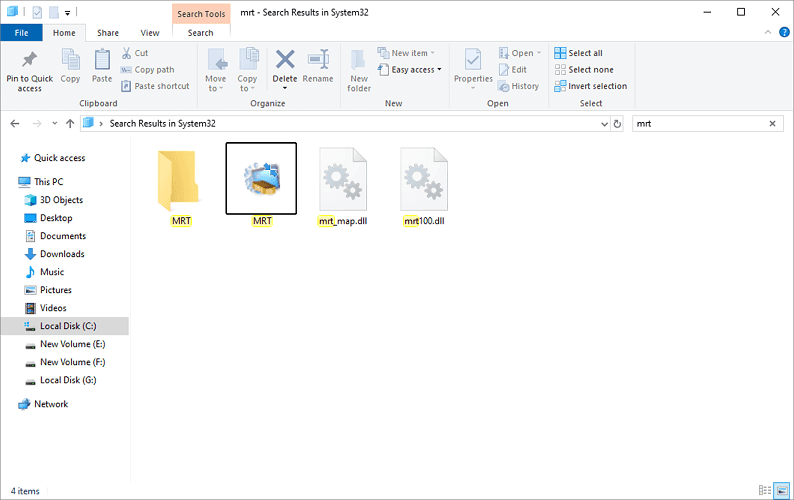
Location of MRT
If it is not found in C:\Windows\System32 folder, it is likely malware disguised as the actual Malicious software removal tool. If it’s not there, search your whole computer drive, making certain to check the search options to “search system folders”, “search hidden files and folders”, as well as “search subfolders”.
Checking its log
Click on Start > Select Run and then type the following string in the Run box %systemroot%\\debug and then click OK > system root > debug. A Windows Explorer dialogue box will open and you ought to a file named mrt.log. You could very well see an additional file named mrt.log.old, which is last month’s log file.
Open up mrt.log with Notepad. You ought to observe something similar to the following:
——————————————————————————–
Microsoft Windows Malicious Software Removal Tool v5.73, June 2019 (build 5.73.16044.1)
Started On Thu Jun 13 10:56:25 2019
Results Summary:
—————-
No infection found.
Successfully Submitted Heartbeat Report
Microsoft Windows Malicious Software Removal Tool Finished On Thu Aug 15 00:14:05 2019
Return code: 0 (0x0)
Based on our observations, as long as this file remains outside of your core system folders, this Windows utility poses no harm.
Delete MRT.exe
If you have an HDD on your computer and are experiencing high CPU and memory usage, removing the MRT file can free up some memory. This file is automatically updated whenever a new Windows update is available, with version 1903 being the latest one.
If you notice through your task manager that this file is consuming a significant portion of your CPU and memory resources, deleting it can provide some relief. However, keep in mind that it is intended to run after updates, so deleting it will be your decision if you find it to be running continuously.
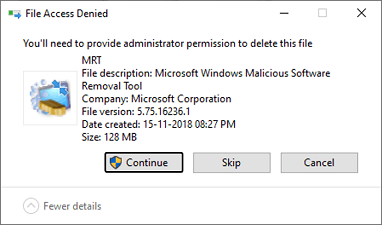
Here’s a step-by-step guide on how to delete MRT.exe if you believe it’s unnecessary on your computer:
- Click on the start button.
- Select my computer icon.
- Select the C drive and tap on Windows.
- Now scroll down until you find the system32 folder.
- Open it and scroll till you find the file MRT.
- Then right-click on MRT and choose Delete.
- Click on Continue to provide administrative authority.
Wrapping up,
In conclusion, we have explored what the MRT.exe file is and highlighted its key features. We also discussed situations where it might pose a risk and its typical location on the system. If you ever feel suspicious about this file, refer to the file log mentioned in the article, and if necessary, consider deleting it.
Should you have any more questions or concerns, please feel free to leave a comment in the section below. We’re here to assist!
