If you have come across the term port 445 or 135, then you are probably a hardcore techie. But if you are reading this article thinking that it is something about USB ports then turn back now.
In this article, we will go over some basic terms concerning all ports in general. Then we will take a deeper look at port 445 and also look at its vulnerabilities and ways to deal with the port.
Contents
What exactly is a port?
The subject of the article is not probably the first thing that comes to your mind when you hear the term ‘Port’. As most of us are only familiar with it from a hardware perspective. In such a case, a port refers to a hole that allows you to connect it to other devices with the help of data cables or chords.
It can be used to access printers, projectors, or such, or to hook your PC to a bigger network. On the other hand, ports mean a different thing when it comes to the software side. But they do somewhat share the same meaning.
The ports that we are talking about are logical constructs within an OS that help to recognize a particular process or network. In simpler words, it is a location to which information can be sent. It can also identify the information that it receives and take necessary actions.
TCP and UDP
You will see these two terms pop up a lot if you are reading about any kind of port. Hence, it is pretty useful to just go over them. Both of these are used for sending pieces of data otherwise called packets. And these packets that they sent go on to reach a specific IP address. The packets cover the journey from your computer to the router to its destination.
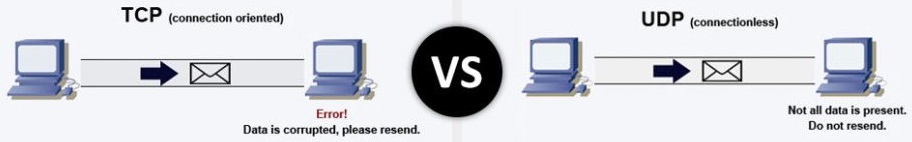
TCP stands for Transmission Control Protocol. This one is working behind most of the things you do with the internet. When you use your browser to enter a page, TCP sends these packets to that server’s address. And if it receives the data, the server returns a stream of data back to the port. This is then rearranged to present the webpage to you. If the other side does not respond, TCP sends the packets again. Furthermore, there is a provision to check for errors as well.
In contrast, a datagram is used in UDP which stands for User Datagram Protocol. The datagram is much similar to the packets of information mentioned above. However, the key difference between TCP and UDP is that it does not check if the other party receives the data or not. It does not account for errors either. Hence it is a lot quicker than TCP. But at the same time, you can say that TCP is more responsible.
What is Port 445?

Port 445 is one of several Microsoft Networking ports that are used today as well as in the older versions of Windows. They were used well with the NetBIOS services in the older versions. Whereas in the newer versions, it is used for direct TCP/IP without the help of NetBIOS.
NetBIOS stands for Network Basic Input/Output System. Basically, it is a program that helps all the computers in a LAN or local area network to communicate with each other. It is also a file-sharing port 445.
Speaking about the port in the discussion, it is used for running Server Message Block (SMB) over TCP/IP in several versions. In any case, the main function of the port is that it serves as a key way of communicating across a Microsoft-based LAN.
SMB Port 445
As mentioned above SMB stands for Service Message Block. This protocol basically lets computers within a network to share information. It is used for a client-server type of communication where the client is the one who asks for the information and the server provides access to it. Such as someone trying to get on a web page and getting access.
Threats against port 445
Though ports are very useful, there exist port 445 vulnerabilities and they are essentially holes in your firewall and security protocols. So open ports mean that there are ways for an outsider to access or corrupt important files in your system. Hackers can use them to spread malware or to exploit vulnerabilities in services or applications.
Port 445 faces several scanning attacks via LAN. And the port is pretty vulnerable and has many weak points. Examples of threats include the appearance of NetBIOS worms and attacks like Wanna Cry.
How to check if port 445 is enabled?
Normally the port is kept open by windows, but you do have to check it on your host. This can be done easily with the help of Command Prompt. Additionally, the Command Prompt can be used for blocking or closing the same port but we will discuss that in the next section.
Follow the steps below to find out if port 445 is enabled or not
- Press the Windows key + R key on your keyboard.
- The run dialogue box opens. In the space provided, type in cmd and then hit Enter or choose OK.
- You can also use the Windows search bar to look for cmd or Command prompt.
- Type the following command and hit Enter: netstat -na
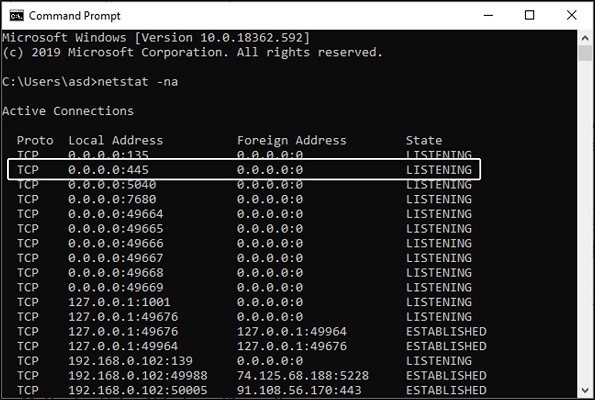
This command does the job of scanning all the ports that are connected. The scan is quite quick and soon the results will show up on your screen. Now look for 445 under the local address column. If its state is shown as “LISTENING” then the port is open.
How to disable port 445 Windows?
Method 1: Using Windows Firewall
This is the simplest out of the three that we are going to discuss down here. Don’t be alarmed by the number of steps though. Because most of them just include a click here and a tap there.
- Go to the Windows Search bar.
- Type in Control Panel and hit Enter.
- Open the app from the search results.
- Out of all the options in this window, choose the System and Security option.
- Choose the Windows Defender Firewall option.
- Now select the Advanced Settings option from the left pane.
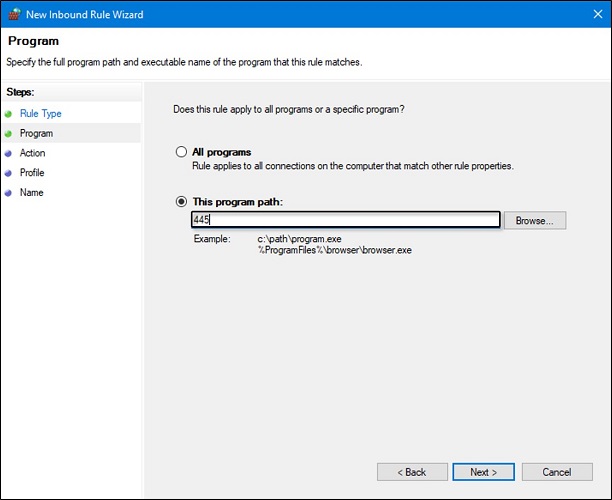
- On the left side of the new window, you will see several tiles. One of them being Inbound Rules. Click it.
- Next, click the New Rule option on the right side.
- A pop window will appear. On that Window, choose the Port option and click on Next.
- Select TCP out of the two options of the former question.
- Choose the specific local ports option for the latter and in the space provided type in 445. Then click on Next.
- Things are much simpler on the next page. Just go for the Block the connection option and then hit Next.
- Tick the three against the three checkboxes and move to the next page yet again.
- Fill in the name and description according to your wish and click on Finish.
- To check the rule you just set up, open its properties.
- Choose the Protocols and Ports tab.
- Check under Local Port.
Method 2: Using Command Prompt
People who have a good handle on using command prompt will find this method more to their liking. The command prompt is a pretty good tool that can be used to run commands on Windows OS.
- Press the Windows key + R key on your keyboard.
- In the run dialogue box type in cmd and click OK.
- Choose to run it as an administrator.
- Alternatively, you can use the windows search bar to look for cmd or Command prompt. Then you can right-click the search result to run it as an administrator.
- Type the following command below and click Enter: Netsh advfirewall set all profile state on
- After that, enter the following command and press Enter yet again.
Netsh advfirewall firewall add rule dir=in action=block protocol=TCP localport=445 name=”Block_TCP-445”
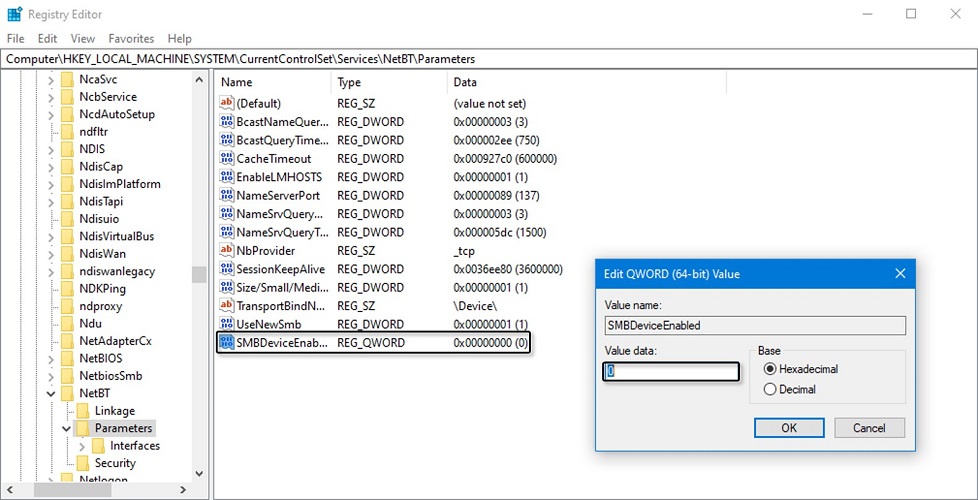
Method 3: Using Registry Editor
The Registry is a database for system files and installed applications. So be careful while messing around with it. If you happen to delete any important files you will be in a bit of trouble for sure.
- Once again open the Run dialogue box by pressing the Windows key + R key on the keyboard.
- Type in Regedit in the space provided and press OK.
- Alternatively, you can use the windows search bar to look for the Registry editor or Regedit. Then you can open it from the search results.
- On the navigation pane on the left side choose open HKEY_LOCAL_MACHINE by double-clicking it.
- Similarly, open the SYSTEM option under it. It is probably going to be near the end of all the expanded files.
- Continue the process along the path as follows: CurrentControlSet\services\NetBT\Parameters
- Now right-click anywhere on the blank area on the right pane and choose New.
- Choose a DWORD (32-bit) Value or QWORD (62-bit) value according to your system (32-bit or 64-bit).
- Set the name of the new value to SMBDeviceEnabled.
- Now right click it and choose the option Modify.
- In the window that appears, change its Value data from 1 to 0.
- Hit OK and you are done.
Wrapping up,
We have discussed a good deal about port 445. By now you probably got a good handle on what the port is, how it is vulnerable, and how to close it. Do keep in mind to know what you are dealing with while you work with ports.
